|
StealthSurfer

There are several issues with this software that have to be noted. These issues may or may not be important depending on the situations the users are presented with while using StealthSurfer. Here is a list of problems that were encountered:
Issues with MojoPac
1. Doesn't work on Windows Vista, Linux, or Mac OS. If you just happen to need to use your StealthSurfer on Vista, you will be presented with and rather displeasing messages telling you that you are unable to run it.
2. Administrative Control issue:
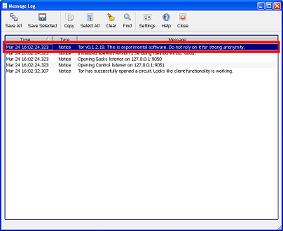
3. Tor Message logs. Aside from being hilarious when a security software that tells you that it is not secure, this might be a real problem for some users.
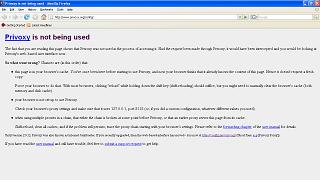
4. If you happen to be on the network on which the administrator limited the ports that can be used to connect to the internet, it will be impossible for you to use Tor. As can be seen to the screen shot when you are sitting on the limited network, Tor doesn't have the ability to communicate with the outside world. The ports can be changed in the Control Panel; however, if the administrator decided to block all of the ports, then it's tough luck trying to find a viable port.
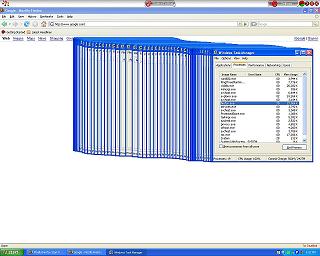
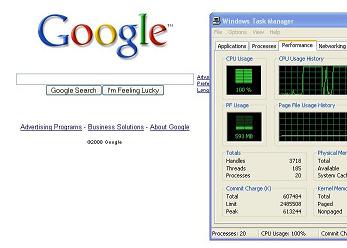
5. Because of its nature, the performance of StealthSurfer largely depends on the environment and the system you are running it in. Naturally the more powerful the system the less problems you will have while running this software.
| System 1 | System 2 | System 3 |
|
|---|---|---|---|
| Processor | Intel Pentium 4 |
Intel Pentium M |
Core 2 Duo |
| Processor Speed | 2.8 GHZ |
1.7 GHZ |
|
| RAM | 1.0 GB |
512 MB |
2 GB |
Memory problems were encountered while running StealthSurfer with 512 MB of
system. On System 1, for some unknown reason Mozila Firefox would a consume most of the processor doing absolutely nothing.
Conclusion
This software largely depends on the user and what it will be used for. On one hand, it could be very handy to have your own mini-PC on your flash drive with excellent security features. On the other hand this software might be useless for you. The overall impression of this software demonstrates that the creators put forth much effort to compile and create the whole system like environment. If you plan on purchasing this software, place great consideration on where and how it's going to be used.