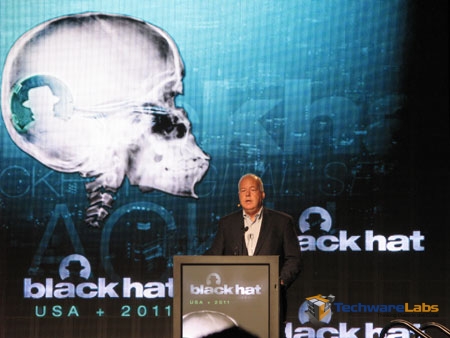
The 15th Black Hat conference is in full swing at Caesars Palace and hot Las Vegas. This years conference is the biggest yet with over 6000 attendees. Jeff Moss, known as The Dark Tangent within inner circles, is the founder of the Black Hat and DEF CON. Jeff opened the first day of the Black Hat briefings welcoming attendees from all over the world including Bulgaria, France, Germany, the Netherlands, and many other countries. During the brief introduction Mr. Moss reminded the attendees that this conference brings together people from many different perspectives with a common goal of securing information. He called on decision makers to let ‘us’ in, and not to wait until ‘the house is on fire’ to call in security experts. The need for info sec early in the decision process is vital to ensure successful business process. With the IP v4 space reaching maximum capacity IP v6 is now on the playing field, which was expected and predicted at last years event.
This years keynote speaker was ex CIA and ex Vice Chairman of BlackWater Cofer Black. Mr Black attempted to compare the emergence of computer security with the development of counter-terrorism efforts in the 1990’s at the CIA. With 28 years experience at the CIA, and part of the administration during the 9/11 terror attacks Mr Black introduced the idea that challenges of counter-terrorism efforts and computer security are very similar. In short the counter-terrorism evolution and evolution of IT both work on the concepts of validating threats, planning the need for defense, and implementing measures to counter & mitigate attacks. The ‘ramp up’ in information security is just starting and we are at the beginning of the internet age. Delayed validation of technology makes it difficult for decision makers to comprehend the need for prevention methods and acquire funding for threat prevention that is unknown. Chaos and confusion can cloud clear judgement and action, similar to a terror attack. A cyber attack may trigger responses similar to the way a terror attack prompts a counter-attack. This new era has seen a shift from traditional ‘boots on the ground’ warfare to a war of information. This will see an increase in cyber attacks spurring counter efforts, which could be physical responses to a cyber event. For example a group compromised a government network and steal intelligence, in response to this event the nation responds with an air strike. This has changed the threat abbreviation from the post-Cold War “CBRN” (Chemical, Bacteriological, Radiological, Nuclear) to the new “KBC”, (Kinetic, Bacteriological, Cyber). Cyber security is still reality new concept to decision makers, whom may have no personal experience with cyber threat assessment, which makes it an uphil battle to validate threat mitigation spending.
Mr Black closed with a reminder that people in this field (cyber/computer security) are the pioneers of this new age. People depend on this community to protect the information and assets of the cyber world. Conferences like Black Hat are necessary advocates for focus on future development and cyber security efforts.