Fake analyst gained access to dozens of US security and intelligence officials using social networking sites to lure in victims such as a senior intelligence official in the US marine corps, the chief of staff for a US congressman and several senior executives at defense contractors, as well as an official from the National Reconnaissance Office. Article follows below:
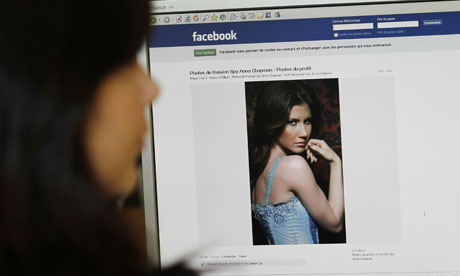
Anna Chapman need never have bothered with moving to Manhattan to become a sleeper agent for the Russian intelligence service. The experience of another femme fatale, Robin Sage, suggests the 28-year-old spy, who posted raunchy photos on her Facebook profile, should instead have honed her social networking skills.
In just a month, Sage made connections with hundreds of people from the US military, intelligence agencies, information security companies and government contractors. The 25-year-old navy cyberthreat analyst was invited to speak at security conferences and offered jobs at companies including Google and Lockheed Martin.
Her Twitter profile proclaimed: “Sorry to say, I’m not a Green Beret! Just a cute girl stopping by to say hey! My life is about info sec [information security] all the way!”
But there was a slight hitch: Robin Sage did not exist. The pretty cybergeek, supposedly educated at the Massachusetts Institute of Technology (MIT) and a prep school in New Hampshire, was in reality an avatar created by a security researcher to find out how social networking sites could be used to covertly gather intelligence.
Thomas Ryan, co-founder of Provide Security, said that despite claiming to have worked professionally for 10 years, Sage attracted dozens of connections across sites including Facebook, LinkedIn and Twitter, including a senior intelligence official in the US marine corps, the chief of staff for a US congressman and several senior executives at defence contractors, as well as an official from the National Reconnaissance Office, which builds, launches and runs US spy satellites.
Many of her new online friends shared personal and professional information and photos, which Ryan claims could have compromised corporate and possibly even national security.
Ryan, who will present his study at the BlackHat security conference in Las Vegas next week, told Computerworld: “I had access to email and bank accounts. I saw patterns in the kind of friends they had. The LinkedIn profiles would show patterns of new business relationships.”
The security analyst told the magazine that the vast majority (82%) of Sage’s online friends were men, suggesting her looks lay behind her popularity. His conclusion after completing the study: “The big takeaway is not to befriend anybody unless you really know who they are.”
[Source]

[…] This post was mentioned on Twitter by ChrisTWL, Cory Blomenkamp, tcpflorida, Tom Gowing, mattandroTWL and others. mattandroTWL said: Review: US Security Chiefs Tricked in Social Networking Experiment – http://www.techwarelabs.com/us-security-chiefs-tricked/ […]